Smarsh-owned TeleMessage suspended its digital archiving services this week following reports of a critical security breach affecting an unauthorized Signal clone utilized by former National Security Adviser Mike Waltz and other high-ranking Trump administration officials. The shutdown occurs as cybersecurity experts warn that the app’s fundamental design may have compromised sensitive government communications by undermining the very encryption it claimed to replicate.
Security Incident Triggers Global Service Suspension
TeleMessage officials confirmed they are currently investigating a “potential security incident” after reports from 404 Media and independent journalists indicated that hackers successfully breached the platform. In response to the detection, the company moved to contain the threat by taking all services offline and scrubbing its website content.
“Out of an abundance of caution, all TeleMessage services have been temporarily suspended. All other Smarsh products and services remain fully operational,” a Smarsh spokesperson stated, adding that an external cybersecurity firm has been engaged to lead the forensic investigation. The company has pledged transparency but has not yet provided a timeline for service restoration.
The Waltz Connection: High-Level Communications Exposed
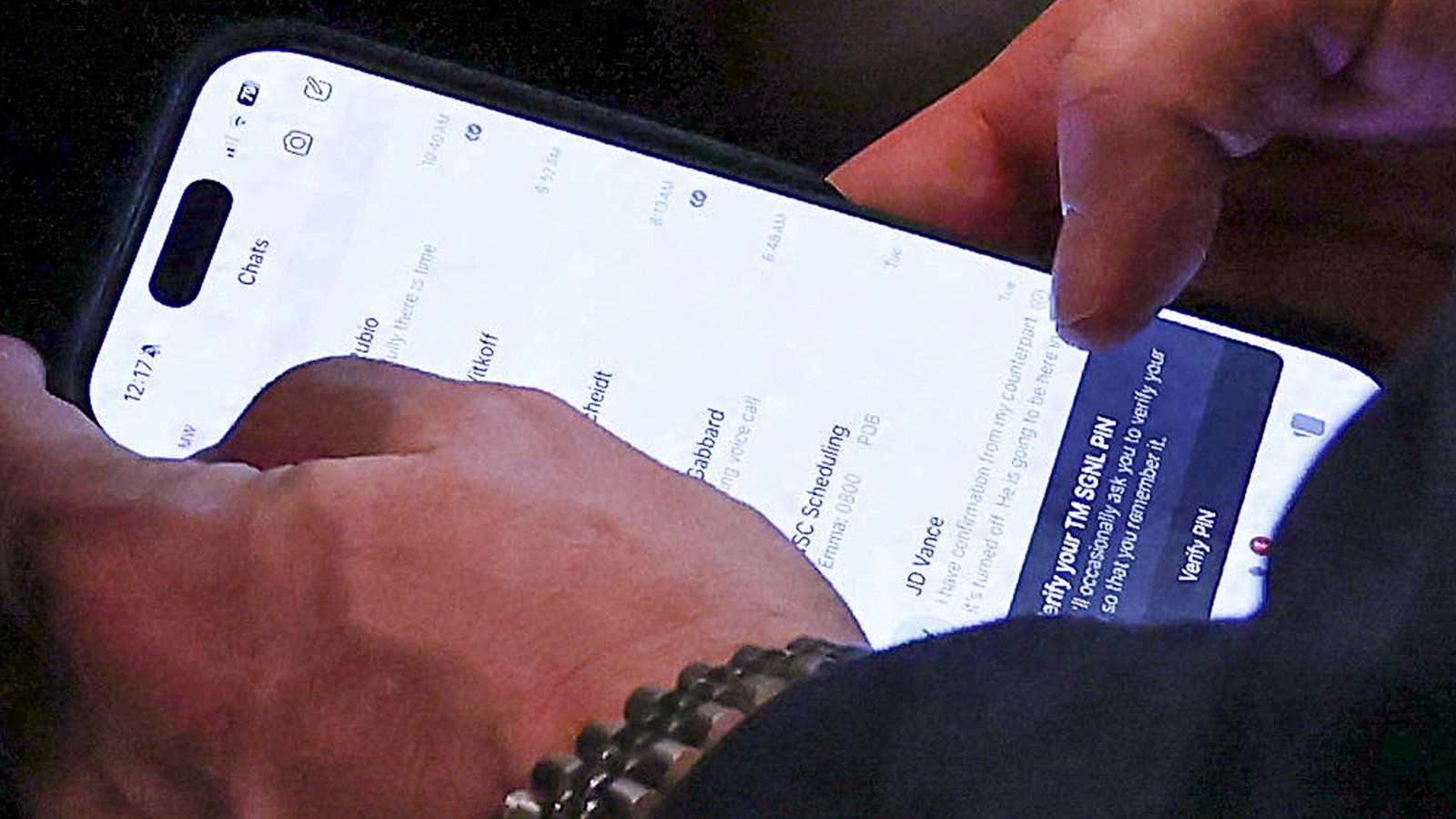
The security failure gained international attention after Reuters photographers captured Mike Waltz using an unauthorized version of the secure messaging app, known as “TM Signal.” These images revealed that Waltz was actively communicating with a circle of high-level officials, including Vice President JD Vance, Director of National Intelligence Tulsi Gabbard, and Secretary of State Marco Rubio.
Waltz’s reliance on the app previously sparked the “SignalGate” scandal, which contributed to his departure as national security adviser. The controversy began when Waltz inadvertently added the editor-in-chief of The Atlantic to a private group chat where administration officials discussed sensitive military operations. Despite the fallout, President Trump recently announced his intention to nominate Waltz as the U.S. Ambassador to the United Nations.
The Fatal Flaw: Archiving vs. End-to-End Encryption
While TeleMessage markets its products as compliant alternatives for institutional use, cybersecurity experts argue that the app’s core feature—communication archiving—is diametrically opposed to the security model of the authentic Signal app. By creating a permanent record of messages to meet regulatory requirements, TM Signal effectively nullifies the end-to-end encryption that prevents third parties from accessing private data.
TeleMessage, founded in Israel in 1999 and acquired by Smarsh last year, claims its “look-alike” apps maintain the same digital defenses as the originals. However, the recent breach suggests these clones may provide users with a false sense of security while creating a centralized honeypot for hackers targeting government intelligence.
Federal Scrutiny and the FedRAMP Compliance Gap
The proliferation of TM Signal within government circles has raised alarms regarding federal digital standards. TeleMessage applications are not approved under the Federal Risk and Authorization Management Program (FedRAMP), the mandatory security assessment for cloud products used by U.S. agencies.
Leaked data suggests the unauthorized use of TM Signal extends beyond the White House to include multiple U.S. Customs and Border Protection (CBP) agents. When questioned about the breach and the potential use of the app by its officers, a CBP spokesperson stated the agency is currently “looking into this.” As the investigation continues, national security experts fear that the data harvested during the breach could jeopardize ongoing operations and sensitive diplomatic relations.